Researchers from Have I Been Squatted, in collaboration with Ctrl-Alt-Intel, reported in February 2026 the discovery of a targeted phishing operation against freight and logistics companies in the US and Europe, which they labeled as Diesel Vortex. According to their data, the campaign was aimed at stealing credentials for industry systems: freight exchanges, carrier and broker portals, as well as payment and fuel circuits, where compromising a login often means direct access to money or the ability to redirect payments.
The only public source of details remains the researchers' publication, while as of the end of February 2026, no confirmations or parallel investigations have been found in major industry and cybersecurity media. This does not refute the facts presented but makes the market perceive the story as a "fresh private investigation" that has not yet gone through the usual mechanisms of independent verification. The details, figures, and mechanics outlined below are based on the report by Have I Been Squatted and partners: description of Diesel Vortex and the restored phishing infrastructure.
According to the report, the confirmed period of campaign activity was from September 2025 to February 2026. Researchers report 3,474 intercepted login/password pairs, of which 1,649 are unique credentials. Telemetry on visits to phishing pages reportedly includes 9,016 unique visitor IP addresses. The infrastructure involved 52 domains, and the list of targeted contact addresses comprised 75,840 emails (57,092 unique). These figures are important not in themselves, but because they show that it was not a targeted attack on a single major player, but an industrial "funnel" with wide distribution, filtering, and active "pressing" of those who clicked.
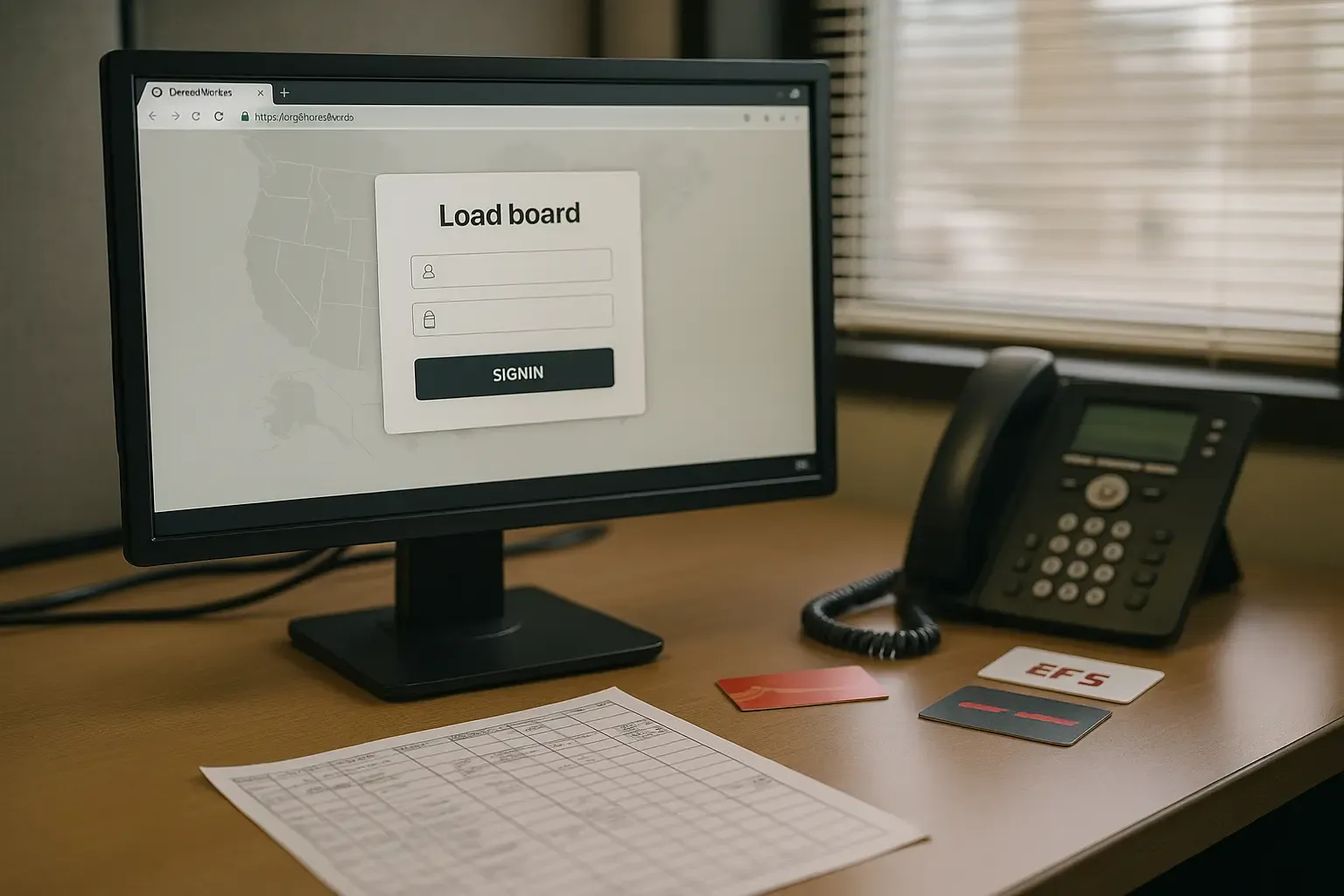
Examples of platforms and processes for which templates were prepared in the report include DAT and Truckstop (the text mentions the phrase "DAT Truckstop"), Central Dispatch, TIMOCOM, Teleroute, Highway, as well as imitation portals of major operators and logistics divisions, including Penske Logistics. A separate section is devoted to schemes around EFS (Electronic Funds Source) — this is not only a risk of data leakage but also a potential ground for check/fuel fraud and payment detail substitution. The report mentions 35 attempts related to EFS checks as a separate observed monetization indicator.
For the industry, the consequences of compromising such accounts usually fall into several scenarios well known to the market: interception or substitution of loading/assignments, access to shipment details and contacts, abuses in "carrier-broker-shipper" communications, double brokering, invoice redirection, and payment instruction changes. When accessing payment and fuel systems, the risks become more direct: from unauthorized issuances/re-issuances to attempts to "withdraw" money through fake confirmations.
Stay Updated with Industry News
Subscribe to our newsletter and get the latest trucking industry news, regulations updates, and career tips delivered to your inbox.
We respect your privacy. Unsubscribe at any time.
A key feature of Diesel Vortex, according to the researchers, is not just the collection of logins and passwords but an "operator in the loop" who guides the victim through the necessary steps in real-time and intercepts one-time codes. The report features signs of voice phishing (vishing) in recovered messages and logs, but the central control channel was Telegram.
The mechanics looked like this: the victim landed on a phishing page, entered their login/password, after which the operator received a notification in Telegram and could initiate additional requests to the victim — for example, ask for a 2FA code, switch the flow to "login via Google/Microsoft/Yahoo," or block the session if something went wrong. This approach targets the most common reality in logistics: many accounts are protected by SMS/TOTP, which works against mass "scripted" attacks but poorly protects against an attack where a person "captures" the code at the moment of its action.
Internal metrics from the report indirectly confirm the manual work of operators: for example, the command/status "Invalid" was used 1,559 times in a dataset of 4,657 requests — meaning operators often rechecked or "caught" the correct password/code in a limited time window.
The report describes a "two-domain" architecture designed to bypass blacklists and browser security mechanisms. From above, the user saw a "decent" domain (often in the .com zone) — a conditional "advertising" domain. But the phishing form itself was loaded inside a full-screen iframe from a second domain — "system," often in the .top or .icu zones. In the researchers' logic, this increased the scheme's resilience: even if the "content" domain is blocked, the "showcase" can live longer, and domain rotation becomes cheaper and faster.
A multi-step "funnel" for filtering out unwanted visitors was then activated. Mentioned are link inclusion planning, template/domain activity switches, IP/ISP/ASN filtering based on ipinfo.io, filtering by user-agents (for bots and sandboxes), parameters and "gates" by URL, ban lists, as well as tokens for the iframe. The report also provides specifics on timings: the browser polled an endpoint like /ajax/check_request.php every second, and the TTL of the token for the iframe was 10 seconds. However, researchers noted an implementation error: the lack of strict control over the maximum lifetime allowed for the forging of "long-lived" tokens.
The report also features "self-defense" metrics of the infrastructure: 254 entries in the IP blocklist (including CIDR and specific addresses), 49 substrings for blocking by ISP/ASN, and 16 patterns by user-agent. Essentially, this reflects the maturity of the phishing platform: attackers clearly anticipated attention from providers, SOC teams, and researchers and pre-built filters against "wrong" visitors.
Another detail significant specifically for the US freight market: in materials recovered by researchers, internal brand designations GlobalProfit and the marketing name "MC Profit Always" appear. The report suggests that "MC" refers to the Motor Carrier (MC number) in the FMCSA system — meaning the creators were clearly thinking in terms of the American market and its familiar carrier identification.
Researchers believe that the platform could evolve into "phishing-as-a-service," i.e., a product for sale to other attackers: ready-made templates for industry services, a control panel, Telegram bots, logging, ban/cloaking, fast domain rotation, plus an operator model for intercepting MFA.
The attackers' resilience was high, but according to the report, they were let down by an operational error: a .git directory was available on one of the phishing sites. This allowed researchers to download the development history and collect almost a complete artifact trail: codebase, database dumps, webhook logs, fragments of internal communications, and change history. The report states that the restored platform included over 2,100 files and a database with 54 tables; a separate key artifact was an SQL dump of 36.6 MB with a timestamp of February 4, 2026.
In the Telegram toolkit, according to researchers, 10 bot tokens were discovered, nine of which remained active at the time of analysis. This is important for practitioners: such a management scheme lives as long as the tokens and channels do, so a token leak can accelerate the "cutting" of infrastructure if providers promptly revoke them.
The report's authors describe the group as "Russian-linked": Russian-language comments are mentioned in the code and documentation, as well as metadata indicating a Moscow context. Simultaneously, Armenian language appears in Telegram logs, and partner Ctrl-Alt-Intel participated in interpreting the relevant fragments. This looks like a mixed operational team or role distribution among participants. The researchers do not name real individuals; only labels/roles of operators in bots and logs (e.g., "Leo operator," "Penske operator") appear, which cannot be interpreted as identifying specific people.
Since there are no independent confirmations of attribution at the time of publication, market participants should perceive the group's "geography" as a working hypothesis of the researchers, not as an established fact by law enforcement.
Even if the specific name Diesel Vortex is set aside, the attack model itself fits well with the current pain points of the industry. Spot recovery and margin struggle accelerate decision-making speed, and thus vulnerability to emails "urgently confirm account," "update password," "check payment." Simultaneously, professional associations in the US publicly emphasize the growing damage from double brokering and payment manipulations and support tightening measures against market fraud. For attackers, stealing credentials for freight exchanges and payment systems is a direct path to the same schemes, only with a higher "conversion" because access appears legitimate.
In practice, this means that for carriers and brokers, the "entry point" to most major losses remains banal: a dispatcher, accountant, or owner-operator's account on a freight exchange or payment service, where they managed to gain not the password but the user's trust — and intercept MFA at the moment of entry.